Anti-doxing guide for activists facing attacks from the alt-right¶
Adapted from this blog post originally published by equality labs, 12017 Sep 1. EqualityLabs.org
Hey Movement Fam,
It is the folks from Equality Labs and we have an urgent Anti-Doxing guide to support the activists who are getting slammed by Alt-right Forces around the country for coming out and resisting Nazis from Charlottesville to Berkeley.
[…] Post Charlottesville, Boston, and the Bay Area Anti-White supremacist marches we are seeing an unprecedented number of doxing attacks on all members of the movements.
This guide has been created to deal with the current issues we are seeing.
- It should be incorporated into your regular digital security practices.
- We know that the escalated activity of the White Supremacists is scary, but…
- the best defense now is one rooted in information, compassion and self-care for ourselves and each other, and…
- a commitment to collective resilence.
With that, we have broken up this guide in terms of background and next steps.
Equality Labs welcome questions at:
- email: equalitylabs@protonmail.com
- upon the twitterplace: @EqualityLabs
What is doxing?¶
Doxing (or “doxxing”) is the violent Internet-based practice of:
- Researching and broadcasting private or identifiable information about an individual or organization
- …in order to harass and traumatize activists from organizing activity.
- Additionally, such attacks can also be accompanied by real world violence and spread disinformation about and individual and/or a movement.
How’s it work, concretely?
- Easier to do than you might think. A wealth of information on the internet is hidden in plain sight.
- Hostile individuals can get this information by searching publicly available databases and social media websites like Facebook, as well as by hacking, and social engineering.
- Alt-right attackers of our colleagues around the country are using their full social media ecosystem both to attack and to spread disinformation.
What to do?
- Adopt best practices to stay safe
- The practices below will help lock you down through the attacks
- You need to maintain these things to keep your digital resilience
- “Security is a process, not a product.”
What this guide covers, and what it doesn’t¶
This is a very specific, tailored guide to a certain type of activity and a certain type of problem (problem: aka “threat”, “adversary”).
- Specifically, it is a very practical, nuts-and-bolts guide to protecting yourself from doxing attacks like those coming out of current “alt-right” activity.
- In this case, your adversaries are fanatics and meanies with a resource level similar to yours.
Sometimes your adversaries will be some random rich person, governments, corporations, local police departments…
- In that case, you would need to do some other things that aren’t covered in this guide.
- There’s overlap – much of the advice would be the same, but also a lot of it wouldn’t.
…image here of the trumpeye
Overview¶
Logistics and human-y stuff
- ✔ CREATE A SELF-CARE PLAN
- ✔ CREATE AN INCIDENT LOG
Techy stuff immediately
- ✔ CHANGE YOUR EXISTING PASSWORDS
- ✔ TURN ON 2-FACTOR AUTHENTICATION (2FA) for all your accounts.
Techy stuff step/day 2
- ✔ FIND OUT WHAT INFORMATION TROLLS CAN FIND OUT ABOUT YOU.
- ✔ CALL YOUR CREDIT CARDS, CELL PHONE PROVIDER, UTILITIES, AND BANK AND LET THEM KNOW YOU ARE A TARGET.
- ✔ INSTALL A VIRTUAL PRIVATE NETWORK (VPN)
- ✔ USE THE TOR BROWSER.
- ✔ INSTALL SIGNAL.
Techy stuff steps/days 3 & 4+
- ✔ WEAN YOURSELF OFF G-MAIL AND BEGIN USING ENCRYPTED E-MAIL.
- ✔ FOR SECURE GROUP CONVERSATIONS USE TALKY.IO OR ZOOM.
- ✔ CHANGE YOUR PRIVACY SETTINGS ON YOUR SOCIAL NETWORKS.
- ✔ KILL ALL ORPHAN ACCOUNTS.
- ✔ USE ALIASES WHEN SIGNING PETITIONS OR SIGN-IN SHEETS FOR MEETINGS.
- ✔ FINALLY SECURE AND BACK UP YOUR HARDWARE.
Final little note – Actually, install Signal immediately. Like right now while you’re reading this.
- It’s incredibly easy and quick. Literally takes 2 minutes to install and set up.
- It’s very effective.
- Everybody should be using it all the time.
- Install Signal! & use it :)
With that, here is our check-list for protecting your identity…
Logistics and human-y stuff¶
✔ CREATE A SELF-CARE PLAN¶
- Create a plan
- Recruit your family and friends to help support you.
- Let them know whats going on, because trolling and doxing can be traumatic and you must prioritize your mental and physical health so that you can outlast these attacks.
We take our lead from our collaborators at Stop LAPD Spying Coalition:
- They talk about adopting a vision of security culture that centers all collective security practices as a form of expressing love and solidarity.
- We all have a sense of it from being marginalized, targeted, activists.
- It’s about harnessing those good instincts with knowledge and practice.
Staying sane in insanity
- This is why it is important, even when you are under attack, to give space to your feelings of anxiety and dread.
- But, do not succumb to them.
- Release them and return to your agency.
- In these situations we can practice a culture of mutual-aid and support around digital security.
A way forward
- We can build power instead of paranoia, and meet people where they’re at.
- From there we can have communities of practice that normalize better practices in a way that is resilient in a crisis.
✔ CREATE AN INCIDENT LOG¶
This is crucial to:
- establish patterns of your attacks and can be useful to…
- compare with other organizers to identify larger patterns within the attacks to…
- identify opponents and their organizations.
A sample log could look like this:
(Just a simple table with four columns: date, time, description, result/recommendation.)
But please feel free to create one that makes sense for you and that you can adapt to your situation. The most important thing is that you:
- keep notes throughout your attack and
- share with your security professional when you can.
If you’re not attached to an org that provides you something like a security professional, then you can either:
- Hopefully, talk to the person who is giving you this presentation :)
- Contact an org like Equality Labs, or
- Security Without Borders or
- EFF’s cooperating techs network cooptechs@eff.org
If you like Equality Labs’ incident log example you can use it as an example. Please feel free to make a copy.
But please note: we recommend that you keep incident logs not in google docs but in an encrypted word processing platform like
- Etherpad on Riseup at https://pad.riseup.net or
- Cryptpad at https://cryptpad.fr
Techy stuff immediately¶
✔ CHANGE YOUR EXISTING PASSWORDS¶
What’s up
- Trolls will be trying their best to get into all of your accounts.
- You can find out if you e-mail is part of any recent hacks at www.haveibeenpwned.com
- This will let you know what level of risk you are at for penetration of your accounts.
After you have made that quick assessment,
- make a list of all of your crucial accounts and
- change the passwords immediately so you have fresh passwords for each.
- Ideally, passwords should be randomly generated (by a computer, not by your human head) &
- should be different for each account (never reuse passwords).
Additionally, if you have time we strongly recommend:
- Use a password manager to generate and store all of your new passwords.
- This will allow you a greater capability to create complex passwords for all of your accounts, while
- limiting you to only have to remember one!
Password manager software recommendations:
- 1password https://1password.com/
- KeePassXC https://keepassxc.org/
- LastPass https://lastpass.com/
✔ TURN ON 2-FACTOR AUTHENTICATION (2FA) for all your accounts.¶
2fa wuts that?
- This means you are adding another verification method when you sign into your accounts.
- This helps A LOT when you have trolls trying to break into your account.
- If they only have your password they will be stopped at the second point of verifcation.
Thinking like the adversary
- When thinking about which accounts you want to add 2FA you have to think like a troll.
- Which accounts do you have that would cause the most damage if it was compromised?
E.g.
- By taking over your e-mail they can release and interfere with your communication, and
- likely gain much sensitive information about you (scan of your passport? driver’s license?).
- By taking over your bank account they wreak havok with your finances, etc.
So if possible lock them all down. When in doubt, lock it down.
- 2FA is available for GMail, Facebook, Twitter, Amazon and more.
- When possible avoid using Text/SMS as your method of verification. This is because texts can be intercepted and so are not as secure as…
- the other commmon method: “OTP” (aka “TOTP”).
- We recommend using Google Authenticator app or an app like Authy or FreeOTP.
- These can generate codes on your phone and can be revoked remotely in the chance that our phone is confiscated, stolen, or lost.
However, text/SMS 2fa is always better than no 2fa! (OTP-2fa > SMS-2fa > no 2fa)
You can find tutorials for 2FA instructions for most of your accounts here:
- https://www.turnon2fa.com/tutorials/
- https://twofactorauth.org
Not going to lie to you, at first you are going to find 2fa a little annoying. But:
- It’s worth it. It really is.
- It will get less annoying pretty quickly as you get used to it.
Techy stuff step/day 2¶
✔ FIND OUT WHAT INFORMATION TROLLS CAN FIND OUT ABOUT YOU.¶
Get a quick idea:
- Search for yourself on DuckDuckGo and try doing this search in incognito mode.
- This will give you a sense of how much data exists about you online to people who are not in your network.
- After that inital search you can go on to looking at all of the data broker sites that trade in our personal livs.
Check your Data leaks and Opt out here:
BeenVerified: https://www.beenverified.com/faq/opt-out/
CheckPeople: http://www.checkpeople.com/optout
Instant Checkmate: https://www.instantcheckmate.com/optout/
Intelius: https://www.intelius.com/optout.php
PeekYou: http://www.peekyou.com/about/contact/optout/index.php
PeopleFinders: http://www.peoplefinders.com/manage/
PeopleSmart: https://www.peoplesmart.com/optout-signup
Pipl: https://pipl.com/directory/remove/
PrivateEye: http://secure.privateeye.com/help/default.aspx#26
PublicRecords360: http://www.publicrecords360.com/optout.html
Radaris: http://radaris.com/page/how-to-remove
Spokeo: http://www.spokeo.com/opt_out/new
USA People Search: http://www.usa-people-search.com/manage/default.aspx
TruthFinder.com: https://www.truthfinder.com/opt-out/
Nuwber: https://nuwber.com/removal/link
OneRep: https://onerep.com/optout
FamilyTreeNow: http://www.familytreenow.com/contact
- While it is hard to get all of the content off, every little bit helps.
- Ultimately, the challenge to get your data off these sites is an uphill battle because there are hundreds of these sites and most organizers have very little time to do this work.
Paid services for urgent circumstances:
- In an urgent case of doxing and if you are simply over capacity in terms of your rapid response then consider using a service like Privacy Duck.
- They are incredible and have been working with activists around the country to scrub their data.
- There is an activist subsdized rate that can be arranged through Equality Labs.
- If you feel like you need this and qualify then please e-mail them: equalitylabs@protonmail.com
Also, Privacy Duck share all their free how-to opt-out videos on their YouTube with detailed, step-by-step instructions at: https://www.youtube.com/privacyduckcom
✔ CALL YOUR CREDIT CARDS, CELL PHONE PROVIDER, UTILITIES, AND BANK AND LET THEM KNOW YOU ARE A TARGET.¶
- Many times trolls will take the online attacks into the physical world by trying to go after your credit cards, utilities, and bank accounts.
- They can access these to try to drain your accounts or worse.
- In a case of raised stakes please call them to let them you are target and they can often add an additional layer of security that can help protect you during this time.
✔INSTALL A VIRTUAL PRIVATE NETWORK (VPN)¶
A VPN is like a layer between you and the big bad internet (the internet is very big & bad). You should use one.
- Helps to privatize your network traffic and bypass filtering happening at your internet service provider.
- It also makes sure that trolls can’t find you by using your IP address.
You can get VPN apps for your phone and also your computer.
- We recommend Private Internet Access and Vypr VPN, but whatever VPN you use…
- always read the privacy policy to make sure your service does not sell, store, or share your data and that they will protect it if engaged by the state.
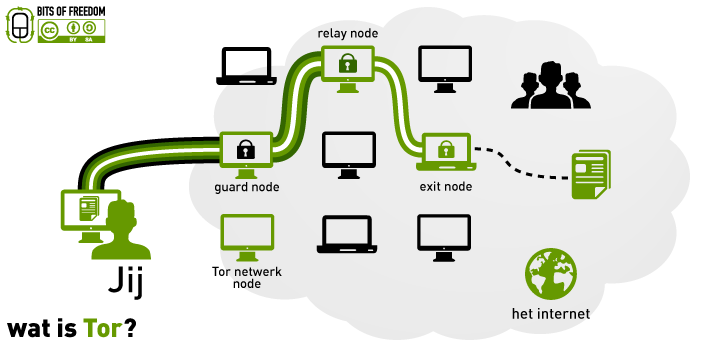
✔USE THE TOR BROWSER.¶
A VPN is great because it can offer privacy but only the TOR Browser offers real anonymity.
This is because rather than going through a VPN’s servers, with Tor:
- your internet traffic is channeled through three random computers
- the software system is designed and setup so all the computers distrust each other (no trust needed)
Using Tor…
- TorProject.org
- Tor Browser is free and provides real anonymity but does not always load multimedia heavy sites.
- Try it out and see!
- We recommend using TOR at least once a day so it becomes part of your daily usage and it won’t be unusual if you have to use it for an urgent situation. (Make privacy normal again :P)
Tor also comes with security downsides:
- Don’t do your banking etc. over Tor!
- Do disable JavaScript when using Tor!
- You can re-enable JavaScript specifically only on httpS (TLS) website connections.
Tor is the only tech that offers real, strong anonymity, but it’s not a tool for everything.
Learn a bit about the tools and know when to use what for what.
✔INSTALL SIGNAL.¶
What is it & how’s it work?
- This secure messaging and voice/video-call app can take the place of text, phone, and e-mail when installed on your phone and computers.
- It’s a lot like texting or WhatsApp.
- Install it on your phone first. Available for Android and iPhone.
- As an extra, verify all the users you are concerned about talking to privately (there is a Verify feature in the app)
- Additionally you can add Signal Messaging to your desktop, by adding it to your Chrome/Chromium browser (install the extension/add-on)
Go get it
- Main website (where you can find how to download): Signal.org
- Handy mini-guide/shameless self-plug: https://medium.com/@sptanager/intro-to-signal-d3bc095a115a
Go get it now. What are you waiting for?
Techy stuff steps/days 3 & 4+¶
✔WEAN YOURSELF OFF G-MAIL AND BEGIN USING ENCRYPTED E-MAIL.¶
G-Mail collaborates with the government on many surveillance programs including the PRISM project. So while Googles extensive protection will help you from individual hackers there is still the inheren threat that all of your data in your account can be searched and stored onto NSA servers with no consent on your part. As a result we recommend if you are using G-Mail use a form of encryption like GPG Encryption for MAC or https://gnupg.org for the PC. These are the safest but the set up of your own GPG can be daunting. In that case use encrypted e-mail services like Tuanota or Proton Mail. We like Tuanota because they are open source and Proton Mail because of its use and scalability. Both services embed your encryption key as part of your service and its interface is similar to g-mail.
✔FOR SECURE GROUP CONVERSATIONS USE TALKY.IO OR ZOOM.¶
All other protocols including freeconference call are not secure. This includes Skype, google hangouts, and facetime. Talky.io is free but can be wonky while ZOOM works but has limited time in its free version. If you are using Zoom make sure you go to the settings and turn on encryption.
✔CHANGE YOUR PRIVACY SETTINGS ON YOUR SOCIAL NETWORKS.¶
Visit your privacy settings for Facebook, twitter, snapchat, and instagram to PRIVATE and block all trolls who already follow you.
FACEBOOK¶
For All of your Facebook privacy settings you can find them here https://www.facebook.com/help/325807937506242/
Key to change are the following settings.
Post visibility
- Change your settings so that only your friends can see your current posts.
- When you want to post something work related as public, set those individual posts as public.
- Protect past timeline posts by watching this video. How To Video. …link…
Friends lists
- If you can review your friends lists.
- Unfriend all those people who follow you or who are your friends but you can’t remember who they are or maybe vaguely remember some awkward interaction with them.
- Double check that each of your friends is unique and no one has created accounts with similar names and photos to a real friend in order to access your private friend only communications.
Other stuff
- Also go through your profile information and make sure your phone number and email are set to be viewed by “only you”.
- Remove featured photos and/or any information in your “About” section in your profile that you would not want to see appear on doxing sites.
- This is because a common tactic trolls will do is to take your album photos and spread them across the internet. They will do this to either create a fake profile for you or to make harassing memes or messages about you.
- Remove your Facebook public photo, and replace it with a generic photo that doesn’t have your actual picture and remove your full birthday (or replace it with inaccurate information).
TWITTER¶
In your Account settings make sure you have verify all login requests so you can flag anyone trying to get into your account.
In your Privacy and Safety Settings make sure you turn off Tweet with a location. This prevents you leaking your location through your twitter statuses.
Turn off photo tagging so that random troll accounts can’t tag you on harassing content or statuses.
Turn off discoverability by e-mail or phone.
If you are concerned about being followed by fake Antifa accounts consider installing an application like block together.
- Through block together you can follow trusted collaborators or accounts who begin blocking Antifa and other hostile sites.
- This is a good practice to build within your own network as you will be able to start to see fake accounts through a pattern of similar messages, bad grammar, or even copy and paste texts.
- Blocking them collectively ensures you can operate with a greater peace of mind because their goals again are to harass and spread disinformation. Once you have installed block together you can subscribe to other users lists to spread community resilence.
- A good one for fake Antifa accounts is the list run by the twitter hand @antifachecker. You can subscribe to their list here: https://blocktogether.org/show-blocks/UQ_ZPDyCHCygI-EUU_6xLY23sewTWFbPA8k7cCdz .
- You can also use services like Troll Busters to attack a troll swarm with affirmative messages that can help drown out the abuse. Learn more at http://www.troll-busters.com.
✔KILL ALL ORPHAN ACCOUNTS.¶
Remember trolls are going to use whatever information they have of you online to get into as many accounts you have.
- Orphan accounts or accounts you have not used in a long time can make you vulnerable because
- if they are using an older password they can try that accounts technical support to
- get more data about you that
- they can try to use for other accounts.
So be on the safe side and shut them down.
✔USE ALIASES WHEN SIGNING PETITIONS OR SIGN-IN SHEETS FOR MEETINGS.¶
One of the number one ways people are getting their names on doxxing lists for the White supremacists is through petion websites and sign sheets.
Our recommendation is to absolutely not use real names, phone numbers or e-mails for these kinds of activities. When possible compartmentalize. Use an e-mail that is only used for their activities that cannot be tied back to your real life details. Additionally for phone consider using google voice or an app like burner app to not divulge your personal information. Finally an alias for these sign up purposes can be your best protection because if they don’t know your name how can they find you.
✔FINALLY SECURE AND BACK UP YOUR HARDWARE.¶
This is going to take some time so take a couple of hours and follow the Equality Labs digital security one sheets here:
https://docs.google.com/presentation/d/1rtWqtbY_tVnncCEEEfRXInN1atSjodloBAaJqRICxAg/edit?usp=sharing
Conclusions¶
OKAY! We know that is a lot but keep in mind. But:
- Digital security is a system.
- You are creating and implementing it as part of your core skills as an organizer.
- There is no silver bullet to digital security, it is an awareness and a practice.
- It gets better with reiteration and with a community committed together to stay safe.
- The best defense now is a collective one and we are all in it together.
So please stay safe and if you have any urgent questions please contact us at:
- email: equalitylabs@protonmail.com
- website at: equalitylabs.org
- the tweetything: @EqualityLabs